All the cyberpunks on the systems of several depending on to their desires and also religions aspire to infiltrate your network, however you can defeat these assaults by delivering an ideal blend of security methods ip booter.
Networks are actually day-to-day threaded with strikes, thus you need to have to offer permanent security. No question that the most popular risks are actually: first, the viruses, which are actually small courses that in reality is attempting to penetrate your system as well as trick the pc, entering it as an add-on with an e-mail notification, beginning promptly after opening the fastened documents, duplicating the very same personal in the system of your computer system. Trojan virus horses which work through the pc by going into the information or even applications documents are beneficial, as well as that is activated on the Trojans after the mediation of certain programs; even begin to take over the reins in the body of your pc.
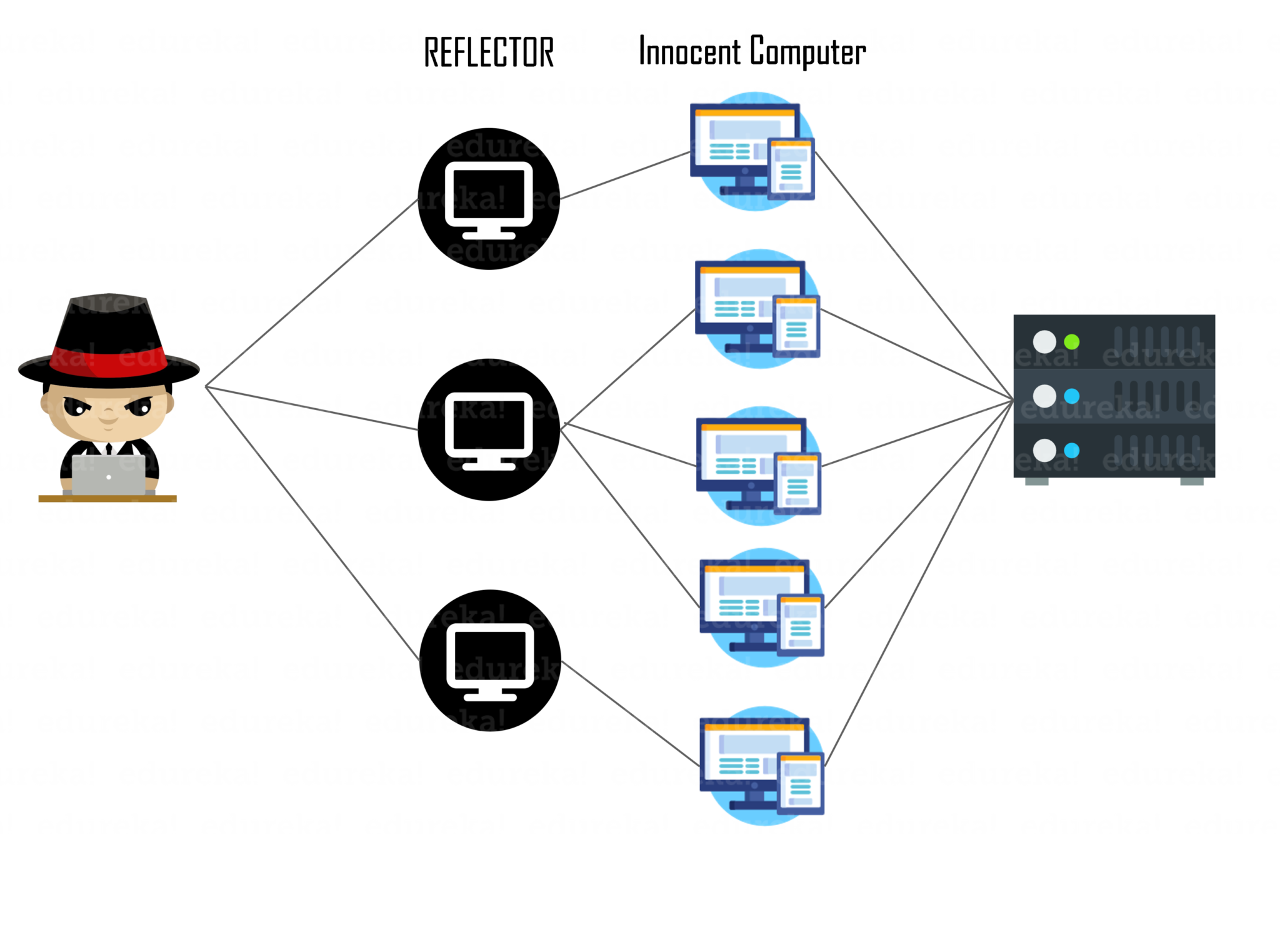
No doubt that these 3 styles of strikes position a primary danger to his business’s data and your personal records. Of program, you don’t prefer or any type of one of the proprietors of companies that their networks are actually factors of assault to circulated rejection of solution assaults.
Is it sufficient to devote hundreds of dollars for the arrangement of firewalls, or even that the expense will amount to numerous manies thousand of dollars? On the wall structures at a minimum required be actually geared up with an examination engine of the records package (SPI), which checks the information of deals of data as well as gives the right of accessibility to your network, in the event it was actually devoid of destructive software application code.
How To Utilize The Firewall Program?
Firewall programs can easily additionally be based on certain regulations or even filters block the action of unsuitable incoming and also outward bound records. It can benefit the selection of World wide web Protocol (IP) for example, as well as to stop existing staff in the system access to the procedure specific handles on the web or even obtaining emails coming from all of them.
Firewall programs may additionally shut out the motion of information in the system based upon an unique identifier named” the headline of control to access to the” (MACINTOSH). A number of firewall programs can easily manage in records by using filters of keywords or scope, and allow records which is actually fated for a specific location. Firewall softwares additionally make it possible for the development of much more innovative to help make more sophisticated rules for the information.
